NIST800-88 Rev 2 Compliant Data Destruction You Can Trust
Trusted by Fortune 500 enterprises and government/aerospace defense contractors alike. Our data sanitization and physical destruction services eliminate risk, ensure compliance, and provide verifiable proof of complete data erasure. Every device. Every drive. Every time.
Comprehensive Data Destruction Methods
We employ multiple destruction methods tailored to your asset type, data sensitivity, and compliance requirements.
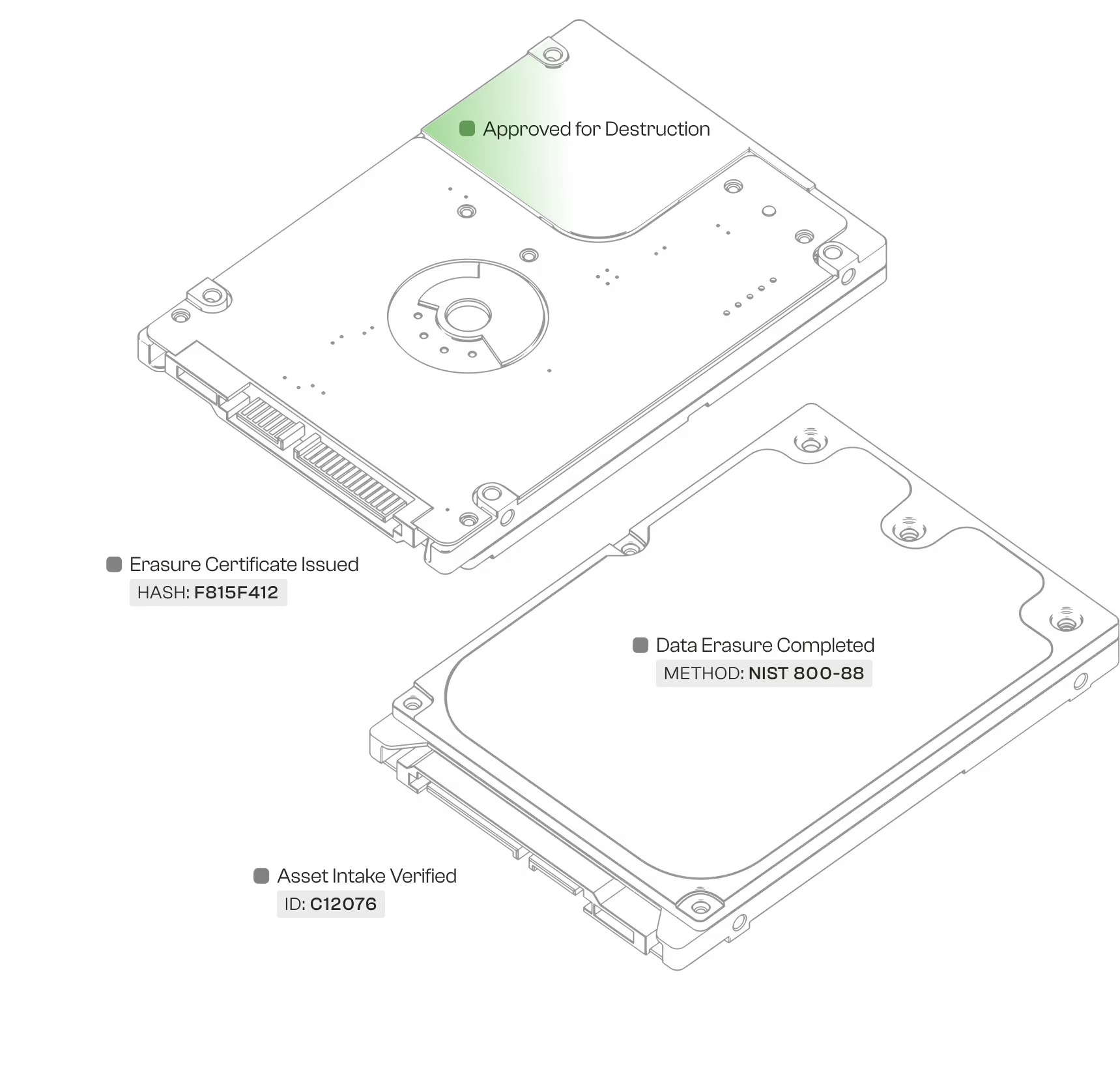
Software-Based Data Sanitization (On-site or at ITAD Tech facility)
Secure data erasure using NIST 800-88 compliant software with multiple overwrite passes. Ideal for functional devices being remarketed. Provides detailed verification reports and certificates.
Degaussing
Magnetic field disruption that renders magnetic storage media completely unreadable. Perfect for hard drives and tape media requiring complete data elimination without physical destruction.
Physical Destruction (Shredding)
Industrial shredding reduces devices to pieces smaller than industry standards require. Ensures data is physically irrecoverable. Required for devices with damaged or non-functional drives.
On-site Data Destruction
Mobile destruction services performed at your facility for maximum security and control. Watch the process in real-time with immediate certificate issuance
Built to Exceed Industry Standards
Our R2v3 certification and comprehensive compliance framework ensure your data destruction meets or exceeds all regulatory requirements.

Healthcare (HIPAA)
Complete PHI protection with sanitization methods approved for medical devices, patient data systems, and healthcare IT infrastructure. Full documentation for regulatory audits.

Financial Services (SOX, GLBA)
Bank-grade destruction meeting SEC, FINRA, and federal banking regulations. Detailed chain of custody and destruction verification for financial data compliance.
Government (NIST, DoD)
DoD-approved methods for classified and sensitive government equipment. NIST 800-88 compliant processes with complete audit trails for federal requirements.
Six Steps to Verified Data Elimination
Data Security Meets Environmental Responsibility
We employ multiple destruction methods tailored to your asset type, data sensitivity, and compliance requirements.
Why Organizations Trust Us with Their Most Sensitive Data
Combining world-class certifications, transparent processes, and verified destruction methods that eliminate risk.


Proven Performance in Data Security
Our track record speaks to our commitment to secure, verified data destruction.
Zero Data Breaches
R2v3-certified protocols ensure permanent data destruction.
Devices Sanitized
Validated through automation and multi-stage quality control.
Expedited Certificate Delivery
Expedited processing available for urgent audits.
Data Destruction Questions Answered
Common questions about our secure data sanitization and destruction services.
Protect Your Data with Certified Destruction
Join thousands of organizations that trust ITAD Tech for verifiable, compliant data destruction. Get your free quote and certificate sample today.